After a pretty basic Session 1, looking forward to focusing in more on OpenStack. We start off with some history and a look at the OpenStack Foundation.
OpenStack started in 2010 as a joint project between RackSpace (providing Swift) and NASA (providing Nova). The role of the OpenStack Foundation is described as:
to promote the global development, distribution, and adoption of the cloud operating system. It provides shared resources to grow the OpenStack cloud. It also enables technology vendors and developers to assist in the production of cloud software.
That’s a bit to abstract for me to understand… but anyway.. also mentioned is information on how to contribute and get help with OpenStack. I think https://ask.openstack.org/en/questions/ will come in very handy. As OpenStack is a community project hopefully I can find something to contribute here – https://wiki.openstack.org/wiki/How_To_Contribute.
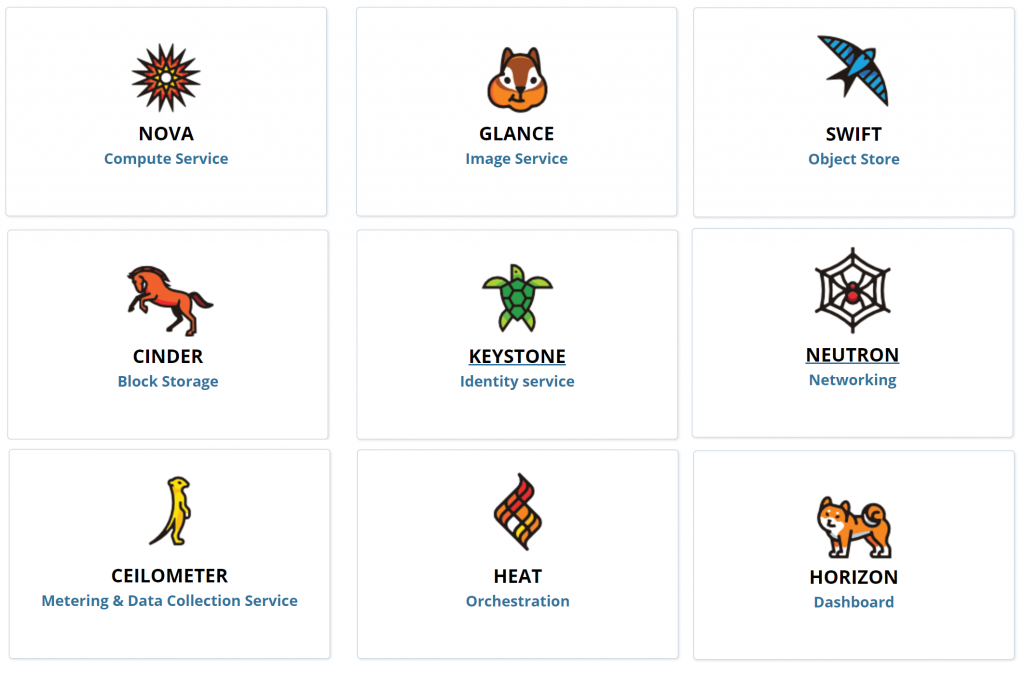
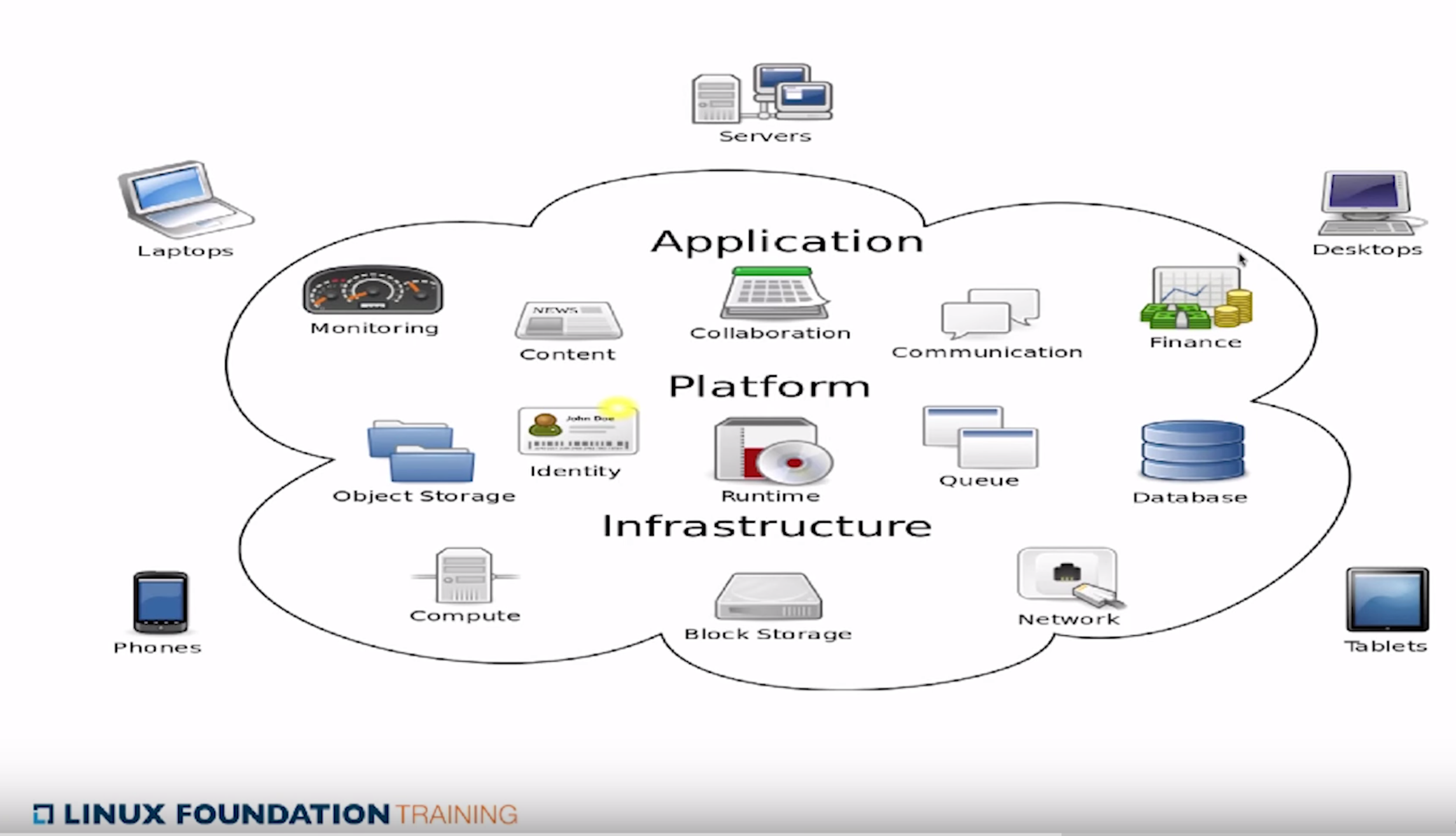
We know start looking at the OpenStack Projects. Being aware of these projects and their maturity status is critical for operating an OpenStack deployment effectively.
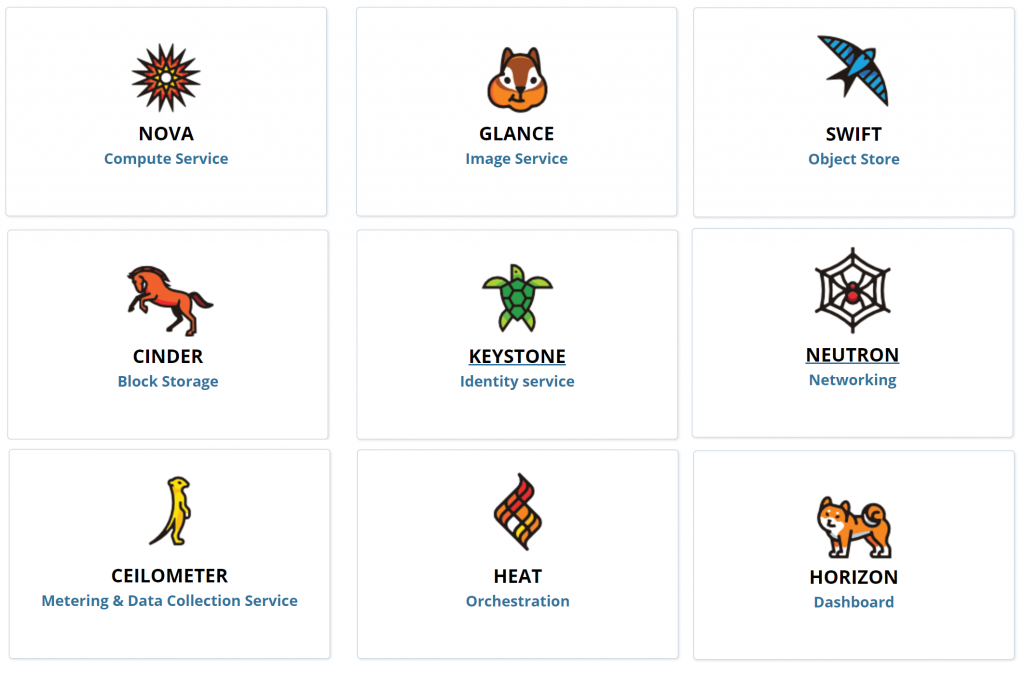
Core OpenStack Projects
There are some other project that have high adoptions rates (>50% of OpenStack deployments):
- Heat – Orchestration of Cloud Services via code (text definitions) and also provides auto-scaling ala AWS CloudFormation
- Horizon – OpenStack’s dashboard with web interface
- Ceilometer – Metering and data collection service enabling metering, billing, monitoring and data driven operations
Other projects introduced in this session:
- Trove – Database as a Service (ie: AWS RDS)
- Sahara – Hadoop as a Service
- Ironic – Bare metal provisioning (very good name!)
- Zaqar – Messaging service with multi tenant queues, high availability, scalability, REST API and web-socket API
- Manila – Shared File System service – Like running samba in the cloud
- Designate – DNS as a Service (backed by either Bind or PowerDNS) – also integrates with Nova and Neutron for auto-generation of DNS record
- Barbican – Secret and Key management
- Magnum – Aims to enable the usage of Swarm, Kubernetes more seamlessly in OpenStack
- Murano – Application catalogue
- Congress – Policy as a Service
After introducing these core services the session delves into a little more detail on the key.
Nove Compute is arguably the most important components. It manages the lifecycle (spawning, scheduling and decommissioning) of all VMs on the platform. Nova is not the hypervisor, it interfaces to the hypervisor you are using (Xen, KVM, VMware, vSphere) via an agent that is installed on the hypervisor. Nova should be deployed in a distributed fashion where some agents run at local work points and some server processes run on the management servers.
Neutron Networking allows users to define their own networking between VMs they have deployed. Two instances may be deployed on 2 separate physical clusters but the user wants the on the same subnet and broadcast network. Though this can’t be done at the physical level, Neutron’s software defined network enable a logical network to be define which transparently configures the underlying network infrastructure to provide that experience to the user. Neutron uses a pluggable architecture meaning most vendors will enable Neutrons SDNs. Neutron has an API that allows networks to be defined and configured.
Swift Object Storage provides highly scalable storage. It is analgous to AWS’s S3 service. Applications running on OpenStack can talk to a swift proxy which stores the data provided to them on multiple storage nodes. This makes it very fault tolerant. The swift proxy is able to make many parallel requests to storage nodes making scalability quite easy. The swift services can be interfaced with via a RESTful api.
Glance Image provides the ability to store virtual disk images. Glance should use Swift/Ceph as a scalable backend for storing the images. A list of ready to download images can be found here: https://docs.openstack.org/image-guide/obtain-images.html – Windows images are available (supported with Hyper-V and KVM hypervisors). An example of deploying an image to Glance (when using KVM):
gunzip -cd windows_server_2012_r2_standard_eval_kvm_20170321.qcow2.gz |
glance image-create --property hypervisor_type=QEMU --name "Windows Server 2012 R2 Std Eval"
--container-format bare --disk-format qcow2 --property os_type=windows
Cinder Block Storage is, in essence, the same as AWS Elastic Block Storage [EBS] whereby persistent volumes can be attached to VMs. Cinder can use Swift/Ceph (or linux LVM) as a backend for storage. Instance storage, without Cinder Block Storage is ephemeral.
Keystone Identity provides authentic and authorization services for OpenStack services. Keystone also provides the central repository for available services and their end points. Keystone also enables definition of Users, Roles that can be assigned to Projects (Tenants). Keystone uses MariaDB by default but can use LDAP (not sure if a DB backend is still required in that case).
Behind the core OpenStack services above – there are some other critical services (dependencies):
- Time synchronization – OpenStack services depend on this for communication, in particular Keystone issues access tickets that are tied to timestamps
- Database – MariaDB (by default) for Keystone is a critical services
- Message Queue – Enable message passing between services – which given the RESTful communications is again critical
Following on from the brief overview of key components of OpenStack we look at the RESTful api – basically just stating that HTTP with JSON is prevalent. If one wanted to basically all OpenStack operations could be complete with cURL.
Horizon is the introduced as a web-based GUI alternative to using the RESTful APIs or the command line client. The command line client can be configure to point to Keystone from which it will discover all the other available services (Nova, Neutron, Swift, Glance etc). The Horizon Dashboard distinguished between Administrators and Tenants but based on our initial testing.
That’s a wrap for, Session 3 we will start deploying OpenStack!